CVE-2022–26134 — Zero-Day Exploitation of Atlassian Confluence
Intro
Atlassian has confirmed a vulnerability reported on May 31st, and assigned the issue to CVE-2022–26134. This vulnerability has been confirmed to affect current versions of Confluence Server and Data Center.
Reference: Volexity
Note: There is currently no available patch or fix for the issue described in this blog post. Volexity strongly recommends that all organizations block external access to their Confluence Server instances immediately until an update is provided by Atlassian.
Atlassian has released an advisory note where this vulnerability has been classified as critical.
CVE-2022–26134
Zero-day exploit that allows unauthenticated remote code execution on the affected servers.
Attackers can execute commands and gain full control of a vulnerable system without credentials as long as web requests can be made to the Confluence Server system.
As detected and analyzed by Volexity attackers can launch a single exploit attempt at each of the Confluence Server systems, which in turn will load a malicious class file in memory. This enables the attacker to effectively have a webshell to interact with through subsequent requests. The “benefit” of such an attack allows the attackers to not have to continuously re-exploit the server and to execute commands without writing a backdoor file to disk.
The initial access detected involves a JSP file, variant of the China Chopper webshell, written into a publicly accessible web directory. Consequently, a series of processes loaded into memory lead to a python script providing an interactive shell to the attacker with root privileges.
Post exploitation activities in the case studied by Volexity involved deploying an in-memory copy of the BEHINDER implant. BEHINDER provides very powerful capabilities to attackers, including memory-only webshells and built-in support for interaction with Meterpreter and Cobalt Strike.
Once BEHINDER was deployed, the attacker used the in-memory webshell to deploy two additional webshells to disk: CHINA CHOPPER and a custom file upload shell.
Protecting Web Servers.
In a previous blog entry we covered how to protect web servers using web application firewalls based on Open Source technologies.
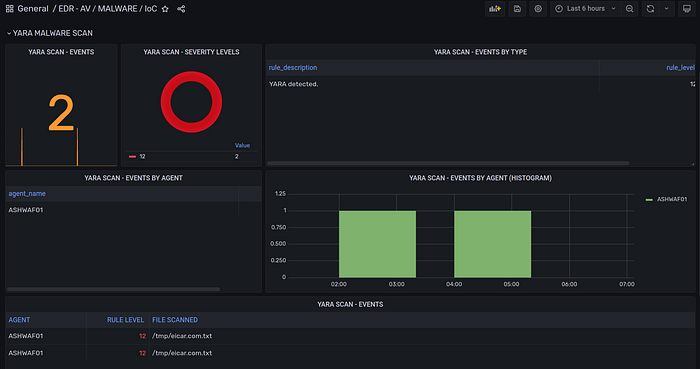
Advanced Malware Scan Using Yara.
Our GitHub repo includes scripts to run malware scan using Yara and alert via Wazuh agent on any files flagged by the Yara rules.
In the case of a web server, the script can be customized to periodically scan the contents of all public web folders.
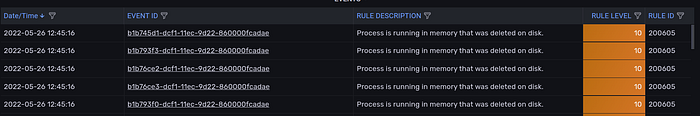
Gathering process telemetry using Osquery will help identifying processes running in memory that were not loaded from existing file images on disk (like in the case of the webshells described above).
Need Help?
The functionality discussed in this post, and so much more, are available via the SOCFortress platform. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Platform Demo: https://www.socfortress.co/demo_access.html
