DNS Traffic Insights using Domain Stats and Wazuh EDR
Intro
Despite being a key part in threat hunting, DNS queries are oftentimes overlooked, if not disregarded, when it comes to analyzing telemetry from the end point and spotting malicious activity.
In this post we cover how to integrate the Domain Name analysis tool “Domain Stats” with the Wazuh stack. All the integration scripts mentioned in this post can be found in our GitHub repo.
Domain Stats
This tool was created by Mark Baggett (SANS instructor). It uses RDAP by default (Registration Data Access Protocol) and is a log enhancement utility that is intended help you find threats in your environment. It will identify the following possible threats in your environment:
- Domain_stats Domains that were recently registered
- Domains that no one in your organization has ever visited before
- Domains with hostnames that appear to be random characters
The domain classification returned by Domain Stats can, in turn, activate a threat intel lookup to check the queried hostname against well known IoCs. In this post we’ll use AlienVault OTX,
After install, it’ll allow you to download the “top1m” and store it in its internal database (SQLite DB used as a “cache”).
Once installed, enables a listener for HTTP conns (port 5730 by default). Calling this API with a hostname/domain as parameter will return valuable information for threat hunting purposes.
Info on how to install and setup this tool can be found here.
Domain Stats & Wazuh SIEM Integration
Requirements:
- A Domain Stats instance up and running.
- Wazuh manager with custom integration as described in our GitHub repo.
- Wazuh Agents with Sysmon (info in our GitHub repo).
Workflow
- Sysmon Event ID = 22 will trigger a custom integration in the manager.
- This integration (Python script) will call the DNS Stats API and will evaluate its response:
- “First time seen” domains / Low Frequency domains / New created domains will generate an alert.
- This new alert will activate an active response script in the agent, who in turn, will make an API call to AlienVault’s OTX passing the queried hostname as parameter.
- If IoCs are found for the specific domain, the agent will insert an alert in its active responses log.
SOCFortress: Domain Stats & Wazuh Integration
Domain Stats — Categories and Events per agent

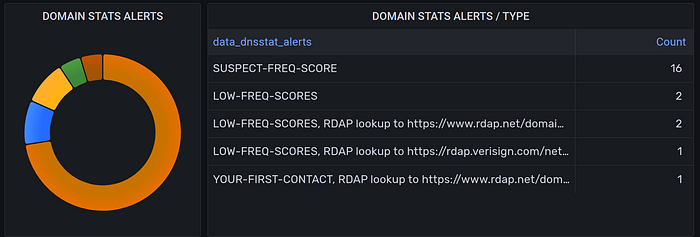
Domain Stats — Alerts by Type
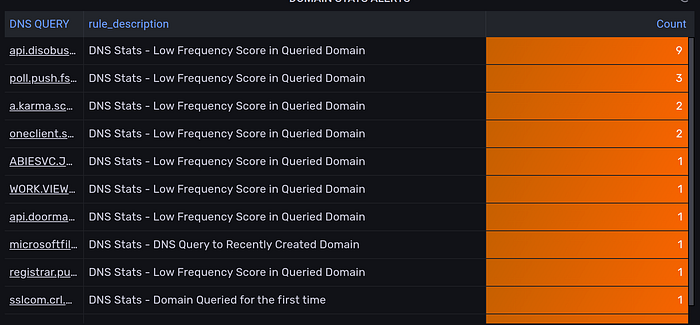
Domain Stats — Queried Hostname and Alert Type
Need Help?
The functionality discussed in this post, and so much more, are available via the SOCFortress platform. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Platform Demo: https://www.socfortress.co/demo_access.html
