Part 4. Wazuh Agent Install —Endpoint Monitoring
Best EDR agent for FREE!
Wazuh Documentation: https://documentation.wazuh.com/current/index.html
Intro
In PART THREE we installed and configured our Wazuh Manager who is responsible for collecting logs from our endpoints for analysis. Now we need to deploy the Wazuh Agent onto our endpoints. The Wazuh Agents multi-platform (Windows, Linux, MacOS, etc.) support and lightweight footprint (35 MB of RAM on average) makes Wazuh the perfect solution for our endpoint monitoring needs.
Keep reading to discover how we can take our log collection to the next level with Sysmon and Packetbeat!
Installation
Installing the Wazuh Agent is straight forward, but lets first understand some basics as to how the Wazuh Agent communicates with the Manager.
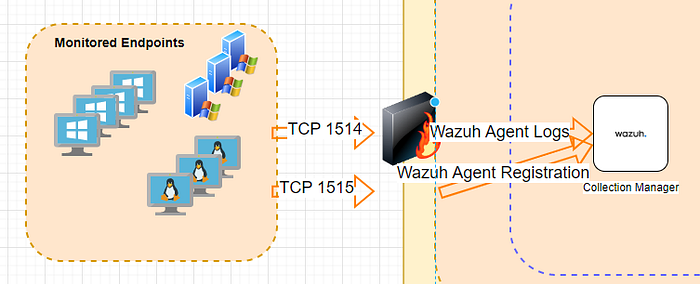
Registration
The Manager and Agent encrypt their communication with one another. To do so, the Manager and Agent must share a client key. This symmetric key encrypts the logs that the agent is forwarding to the Manager.
When the Wazuh-Agent is first started, it will ask for a client key from the Manager (TCP 1515). If authentication is required, password auth or cert auth, the Manager will verify the agent and if approved, will generate a client key that it will pass back to the agent.
Log Forwarding
The Wazuh Agent will now forward logs to the Wazuh Manager. This traffic will travel from the Agent to the Manager on TCP port 1514. Ensure the appropriate firewall rules are in place for both the registration and log forwarding prior to rolling out a mass install.

Agent Install
Wazuh has put together a cool tool for us to use through the Wazuh Web APP to build our single line install command. This will install the agent onto our endpoint and point to to use our manager.
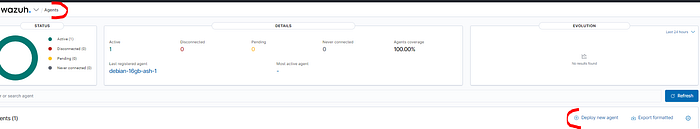

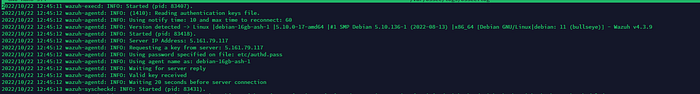
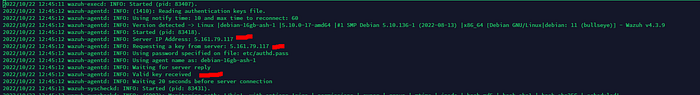
Lets take our install command to our Debian 11 box:
curl -so wazuh-agent-4.3.9.deb https://packages.wazuh.com/4.x/apt/pool/main/w/wazuh-agent/wazuh-agent_4.3.9-1_amd64.deb && sudo WAZUH_MANAGER='5.161.79.117' WAZUH_REGISTRATION_PASSWORD='pleasesubscribe' WAZUH_AGENT_GROUP='Linux' dpkg -i ./wazuh-agent-4.3.9.debNotice we are first grabbing our package installer with curl .

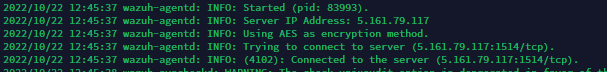
Check your ossec.log file to ensure registration and startup are not presenting any errors and a successful connection to the Manager was established.
Windows
For a Windows install, lets open up PowerShell and run our single line install command:
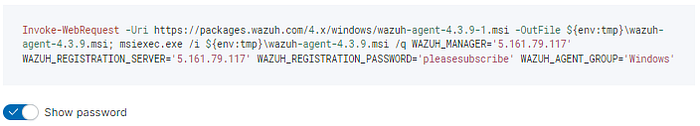
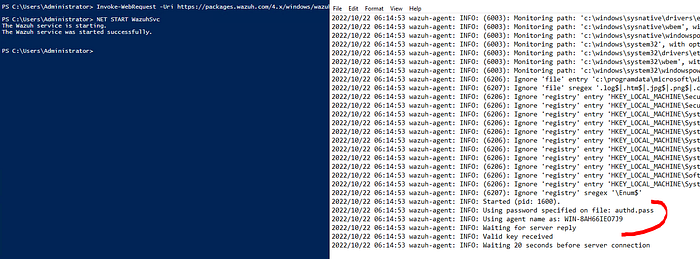
You can bundle these install commands into your own kickstart scripts for a mass rollout across your endpoints!
Next Level Collection
By default, the Wazuh Agent collects Windows and System logs. This is a good starting point but does not provide no where near enough insight into our endpoint activity. Our EDR solution must collect network connections, process spawns, commands ran, etc. for us to accurately detect malicious activity.
The beauty of our Wazuh Agent is that we have the flexibility to deploy other services, such as Sysmon and Packetbeat, to collect more insight into our endpoints. We simply point our Wazuh Agent to these log entries and he will take care of the rest!
Sysmon Install
Let’s install Sysmon on our Windows endpoints. Sysmon is our Windows logs on steroids and is highly recommended for all Windows Endpoints. You can provide your own Sysmon Config file, but in this demo I will be using olafhartong GitRepo: Sysmon Modular
See the below PowerShell script to easily install Sysmon on your own endpoints!
Sysmon is now writing events to Microsoft-Windows-Sysmon/Operational within Applications and Services Logs .
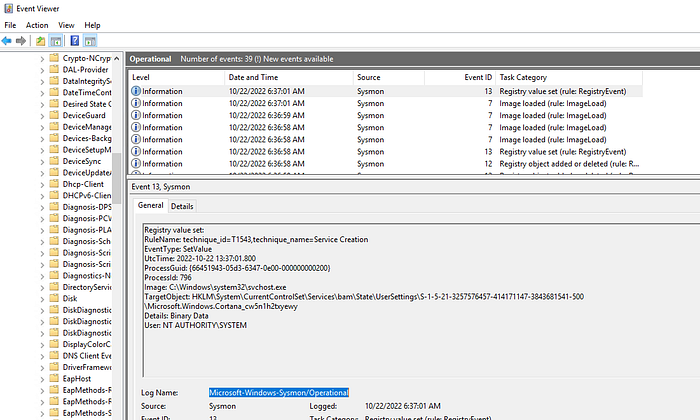
Adding the <localfile> configuration block to our Wazuh Agent’s group (See PART Three) instructs the Wazuh Agent to collect our Sysmon events.
<localfile>
<location>Microsoft-Windows-Sysmon/Operational</location>
<log_format>eventchannel</log_format>
</localfile>
Our Sysmon Logs can now be fed into our SIEM stack:
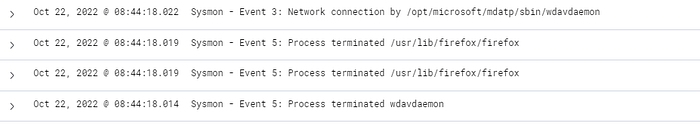
MISSING THESE EVENTS? ENSURE YOUR WAZUH MANAGER CONTAINS SYSMON DETECTION RULES: SOCFortress-Wazuh-Rules
Packetbeat Install
We can use Packetbeat to analyze network traffic in real time! Deploying Packetbeat onto our Linux Endpoints (Sysmon for Windows already collects network traffic) allows us to analyze network traffic traveling to and from our endpoints.
See the below bash script to quickly install Packetbeat!
Packetbeat is now writing its logs to /tmp/packetbeat/packetbeat .
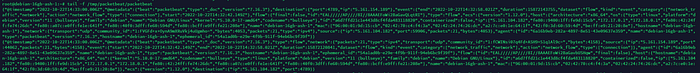
Adding the <localfile> configuration block to our Wazuh Agent’s group (See PART Three) instructs the Wazuh Agent to collect our Packetbeat events.
<localfile>
<log_format>json</log_format>
<location>/tmp/packetbeat/packetbeat</location>
</localfile>
Our Packetbeat Logs can now be fed into our SIEM stack:
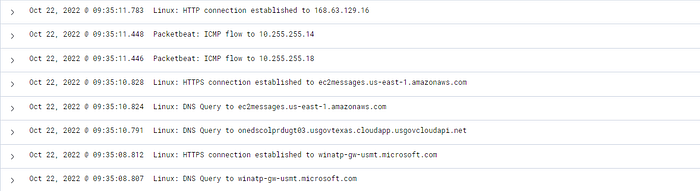
MISSING THESE EVENTS? ENSURE YOUR WAZUH MANAGER CONTAINS SYSMON DETECTION RULES: SOCFortress-Wazuh-Rules
Conclusion
The Wazuh Agent is a powerful EDR agent. The ability to build onto the Wazuh Agent with additional services such as Sysmon and Packetbeat give our SOC analysts full insight into the endpoints. And it doesn’t stop there, we can pull logs from other applications such as Nginx, Modsecurity, MySQL, etc. to provide even more visibility! Try it out for yourself, Happy Defending 😄.
Need Help?
The functionality discussed in this post, and so much more, are available via SOCFortress’s Professional Services. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Professional Services: https://www.socfortress.co/ps.html
