SOCFortress Integrations — Advanced Traffic Flow Analysis using Zeek
Intro
Security teams generally depend upon four sorts of data sources when trying to detect and respond to suspicious and malicious activity. These include:
- third party sources such as law enforcement, peers, and commercial or nonprofit threat intelligence organizations.
- network data.
- infrastructure and application data, including logs from cloud environments.
- endpoint data.
Zeek is primarily a platform for collecting and analyzing the second form of data — network data.
When looking at data derived from the network, there are four types of data available to analysts. As defined by the network security monitoring paradigm, these four data types are:
- full content.
- transaction data.
- extracted content.
- alert data.
Using these data types, one can record traffic, summarize traffic, extract traffic (or perhaps more accurately, extract content in the form of files), and judge traffic, respectively.
NIST 800–53 Controls related to Network Security

About Zeek
Zeek is a passive, open-source network traffic analyzer. Many operators use Zeek as a network security monitor (NSM) to support investigations of suspicious or malicious activity. Zeek also supports a wide range of traffic analysis tasks beyond the security domain, including performance measurement and troubleshooting.
The first benefit a new user derives from Zeek is the extensive set of logs describing network activity. These logs include not only a comprehensive record of every connection seen on the wire, but also application-layer transcripts. These include:
- all HTTP sessions with their requested URIs, key headers, MIME types, and server responses.
- DNS requests with replies.
- SSL certificates.
- key content of SMTP sessions.
- and much more.
Zeek Sensors Deployment
Zeek sensor(s) are typically deployed using a network tap in the core switches. A dedicated network port in the switch will mirror one or more up-links and will send all the mirrored traffic to the Zeek sensor.
The sensor needs a second network interface to connect to the corporate network and forward the collected events.

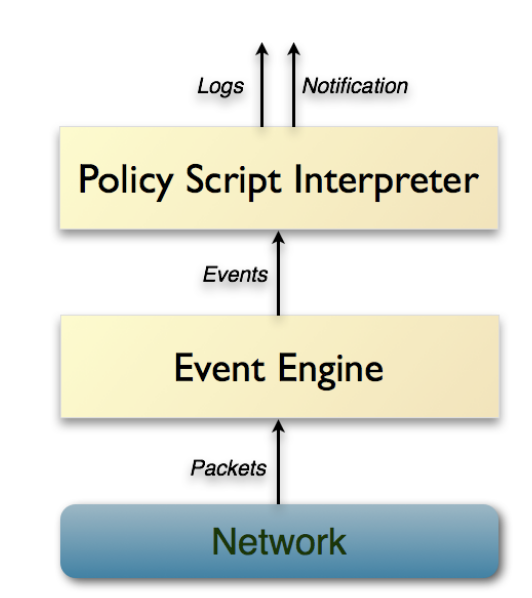
At a very high level, Zeek is architecturally layered into two major components. Its event engine (or core) reduces the incoming packet stream into a series of higher-level events. These events reflect network activity in policy-neutral terms, i.e., they describe what has been seen, but not why, or whether it is significant.
Semantics related to the events are derived by Zeek’s second main component, the script interpreter, which executes a set of event handlers written in Zeek’s custom scripting language. These scripts can express a site’s security policy, such as what actions to take when the monitor detects different types of activity.
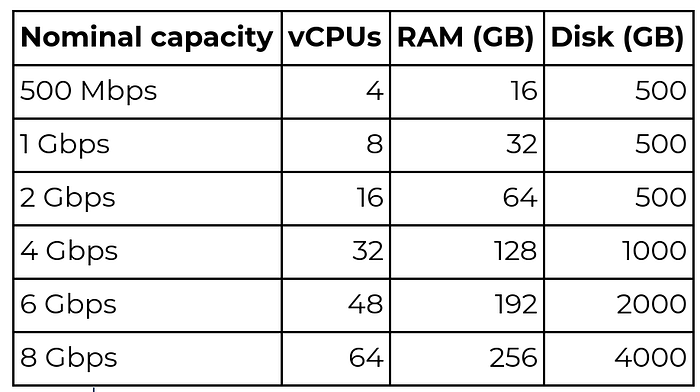
Zeek Sensors — Dimensioning (guidelines)
Zeek Logs and SOCFortress’ Threat Intel
Collected events can be analyzed using the native intelligence framework included in Zeek. The goals of Zeek’s Intelligence Framework are to consume intelligence data, make it available for matching, and provide infrastructure to improve performance and memory utilization.
Data in the Intelligence Framework is an atomic piece of intelligence such as an IP address or an e-mail address. This atomic data will be packed with metadata such as a freeform source field, a freeform descriptive field, and a URL which might lead to more information about the specific item. The metadata in the default scripts has been deliberately kept to a minimum.
The way SOCFortress incorporates threat intel analysis though is by leveraging our existing threat intel APIs. The metadata recorded by Zeek that will be analyzed by our threat intel modules includes:
- Public Source and Destination IP Addresses.
- DNS queries.
- File hashes (SHA256).
Visualizations and Traffic Analysis
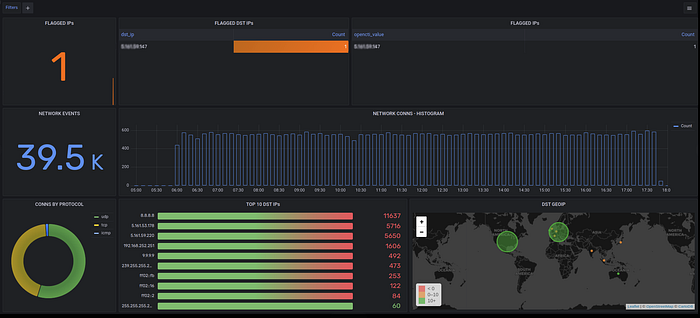
All network connections
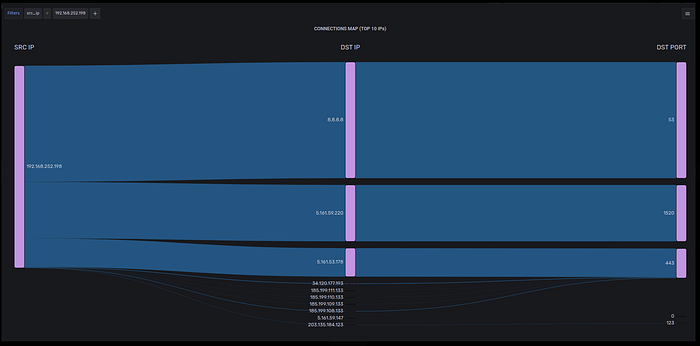
Network Maps
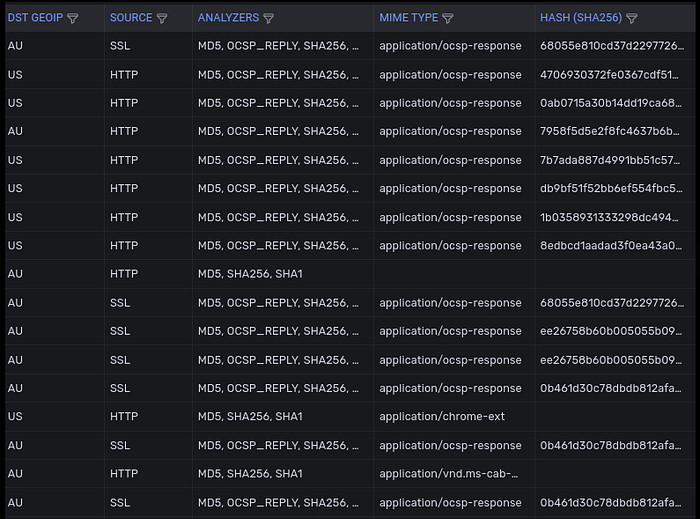
Files and File Hashes
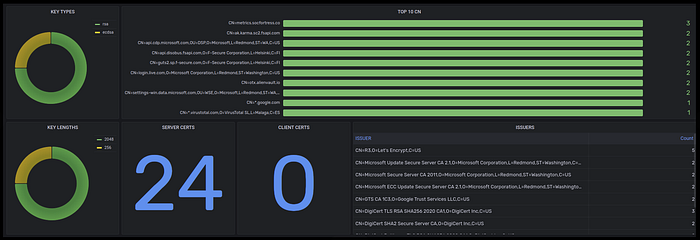
SSL Certificates
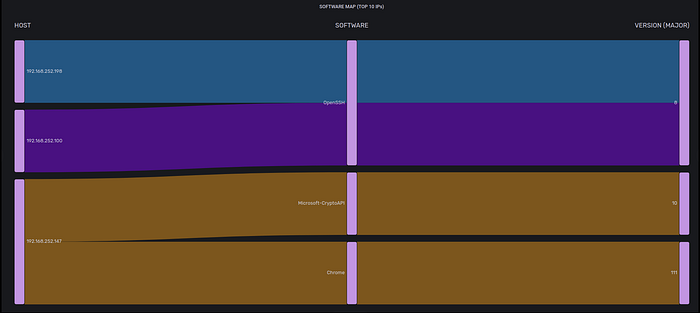
Detected Software
Need Help?
The functionality discussed in this post, and so much more, are available via the SOCFortress platform. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Contact Us: https://www.socfortress.co/contact_form.html








