SOCFortress Integrations — Kaspersky EndPoint Protection
Intro
Kaspersky Endpoint Protection is a comprehensive security solution designed to protect endpoints such as workstations, servers, and mobile devices from various cyber threats.
Kaspersky offers a range of features to safeguard endpoints and prevent unauthorized access, malware infections, data breaches, and other security incidents.
SOCFortress integrations and visualization tools allow security analysts the visualization and triage of these security events using a single pane of glass.
About Kaspersky
Some key features and capabilities of Kaspersky Endpoint Protection include:
Antivirus and Antimalware: Kaspersky provides real-time protection against viruses, malware, ransomware, spyware, and other threats. It uses signature-based detection as well as advanced heuristic and behavioral analysis to identify and block malicious files.
Firewall: Built-in firewall that monitors network traffic and controls inbound and outbound connections. The firewall helps protect against unauthorized access and blocks suspicious network activity.
Web Protection: Web filtering and URL reputation services to block access to malicious or inappropriate websites. It can help prevent phishing attacks, drive-by downloads, and other web-based threats.
Device Control: This feature allows administrators to define and enforce policies for connected devices (USB drives, external storage, etc.) to prevent unauthorized data transfer or the introduction of malicious code through removable media.
Application Control: Kaspersky can restrict the execution of unauthorized applications based on whitelisting or blacklisting rules. It helps prevent the execution of malware or unauthorized software.
Ingesting Kaspersky Security Events
Kaspersky includes a syslog forwarder that enables exporting all registered alerts and security events in their management portal to external systems, such as log collectors or SIEMs.
Configure Kaspersky to generate event logs:
Using Kaspersky administration console, enable the logging feature and configure it to generate event logs for the desired events. Refer to the Kaspersky documentation for specific instructions on enabling and configuring event logging.
Set up log forwarding from Kaspersky to your network log collector:
Kaspersky supports several ways and formats to forward logs to a log collector system:
Syslog: Configure Kaspersky to send logs using the Syslog protocol, which is commonly supported by log collector sytems. Specify the SIEM system’s syslog server address, port, and any required authentication details in the Kaspersky settings. As per log message format, Kaspersky supports CEF, which is a good option in many cases.
Configure your log collection system to receive and process the forwarded events: Once the log forwarding mechanism is in place, configure your SIEM system to receive and process the forwarded events from Kaspersky. This typically involves setting up a log source or data input configuration within the SIEM system, specifying the log format and source details (e.g., syslog server, port, or log forwarding agent details).
Visualizations and Events Details
Alerts:
Kaspersky EndPoint Protection will generate alerts when several conditions are detected, including:
Virus or Malware Detection: Kaspersky’s antivirus software alerts users when it detects a virus or malware. It provides information about the infected file or application and offers options to quarantine or remove the threat.
Suspicious Activity: Detect and alert users about suspicious activities on their computer, such as unauthorized access attempts, unusual network traffic, or suspicious behavior by applications or processes.
Firewall Alerts: Kaspersky’s firewall component monitors incoming and outgoing network traffic. It can generate alerts when it detects unauthorized network connections or suspicious activities that may indicate a potential security breach.
Updates and Software Status: Notifies users when software updates or patches are available to ensure that their systems are protected with the latest security fixes.
These are some of the common types of alerts that Kaspersky products may generate. The specific alerts and features available may vary depending on the version and configuration of the Kaspersky software you are using.
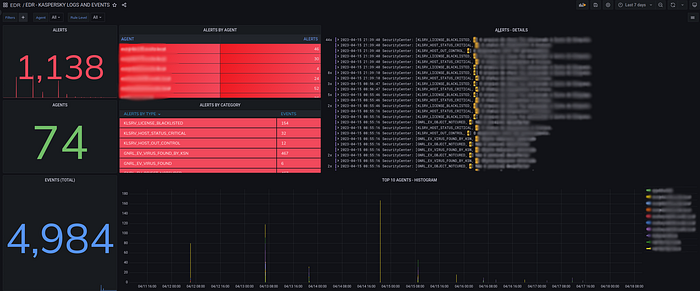
All these alerts will be summarized and displayed in SOCFortress’ dashboards and panels. It’s also possible to access and analyze all the metadata included in every alert.
All events:
Besides high severity events, all events available in Kaspersky management console, regardless of their impact or severity level, are also available for visualization and analysis.

Need Help?
The functionality discussed in this post, and so much more, are available via the SOCFortress platform. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Contact Us: https://www.socfortress.co/contact_form.html
