Using Wazuh Stack to run Network Scans
Intro
Wazuh and NMAP integration to scan network subnets for open ports and services.
In this integration we’ll use python-nmap (https://pypi.org/project/python-nmap/) to scan for open ports/services found in different subnets.
NMAP port scanners can be installed in different Wazuh agents placed in different network segments. The NMAP output is converted to JSON and appended to each agent’s active responses file.
The scan can be scheduled via chrome job to be executed once a week, month, etc. It can also be triggered using Wazuh’s wodle command integration.
Requirements
- NMAP installed in every agent to run the network scan.
- python-nmap (https://pypi.org/project/python-nmap/) installed.
Python-nmap
Python-nmap is a python library which helps in using nmap port scanner. It allows to easilly manipulate nmap scan results and will be a perfect tool for systems administrators who want to automate scanning tasks and reports. It also supports nmap script outputs.
Python script run on agents
Scripts and detection rules (Wazuh Manager) can be found here
Network Scan
Summary of network scans run by all Wazuh agents
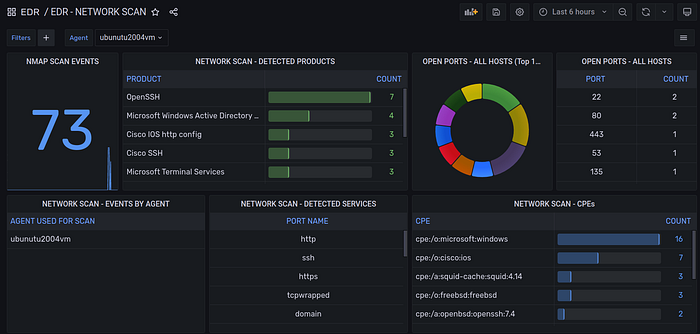
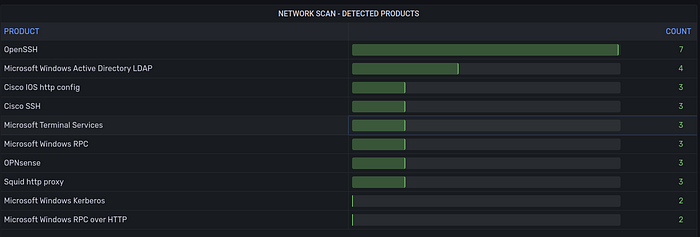
Detected software products opening network sockets:
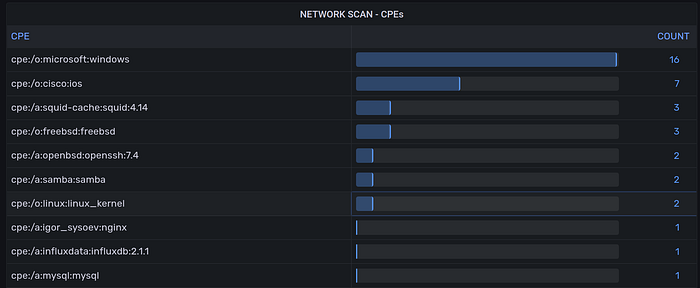
CPE info on scanned hosts:
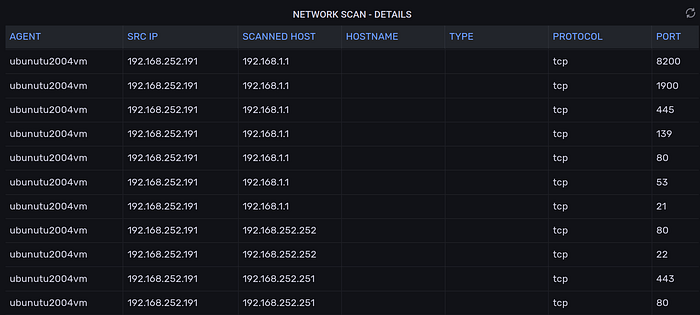
Full events table
Need Help?
The functionality discussed in this post, and so much more, are available via the SOCFortress platform. Let SOCFortress help you and your team keep your infrastructure secure.
Website: https://www.socfortress.co/
Platform Demo: https://www.socfortress.co/demo_access.html
